I Don’t Really Need Cybersecurity Insurance – Do I?
- Apr 15, 2020
- 4 min read

Your data is under attack. You’ve seen this in the news with the Equifax and Target breaches – and the number of data breaches is increasing. This means your business has a higher likelihood of being attacked today than in years past. For this reason, you need Cybersecurity Insurance.
What is Cybersecurity Insurance?
Cybersecurity Insurance is designed to mitigate losses from a variety of cyber incidents including data breaches, business interruptions, and network damage. Many companies forego available policies citing the perceived high cost of policies, confusion about what they cover, and uncertainty that their organizations will suffer a cyberattack. In recent years, the Department of Homeland Security National Protection and Programs Directorate (NPPD) has engaged key stakeholders to address this emerging cyber risk area.
Every Business Needs Cybersecurity Insurance Today.
I hear you saying this now – “But my business is small. Hackers won’t attack it.”
Every business has data that can be damaged or stolen, even small ones. Hackers are especially targeting small businesses because their security isn’t as extensive as it is for larger enterprises.
Nationwide Insurance conducted a survey of 1,069 businesses with 1 to 299 employees. Here’s what they found:
50% reported that they’ve been hit with a cyberattack.
30% said their computers were infected by a virus.
29% suffered from phishing attacks.
13% got Trojan Horses.
12% were hacked.
7% had their data breached.
20% of Cyberattack Victims spent at least $50,000 and required longer than 6 months to recover. 7% spent more than $100,000.
Some business owners say: “But I don’t sell anything online.”
Every business is at risk for a data breach, not just e-commerce businesses.
Here’s what you should be asking:
“What is my risk?”‘
Laptops
Smartphones
Working from home
Payment processing and skimming
Hacking into your system
Employee negligence
Email
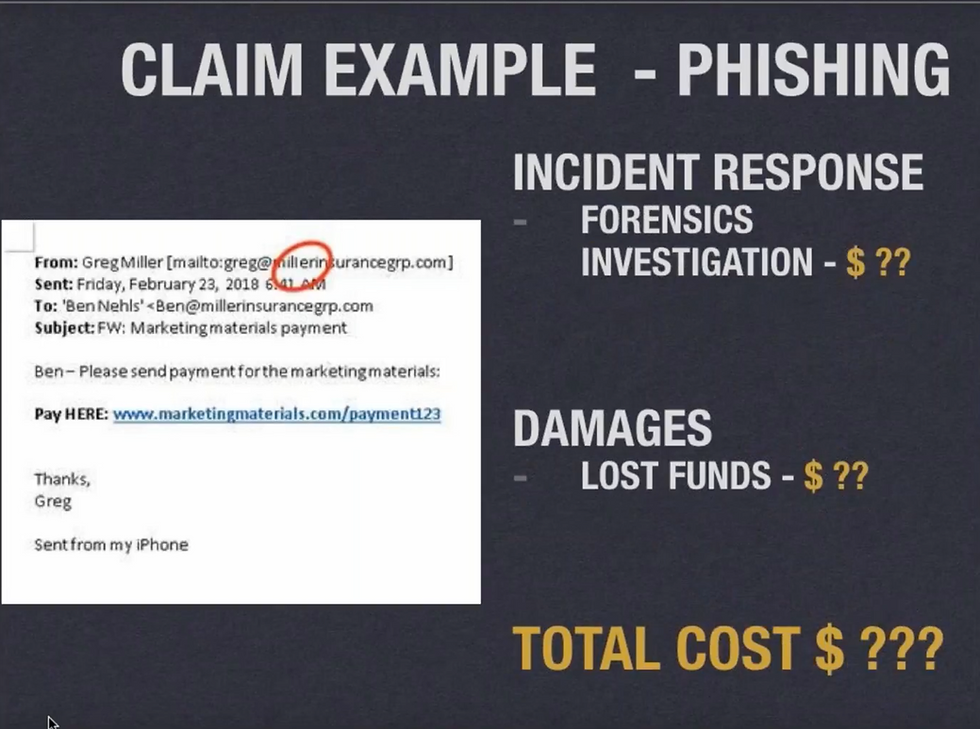
Phishing
Proprietary information
SoftwareSensitive information
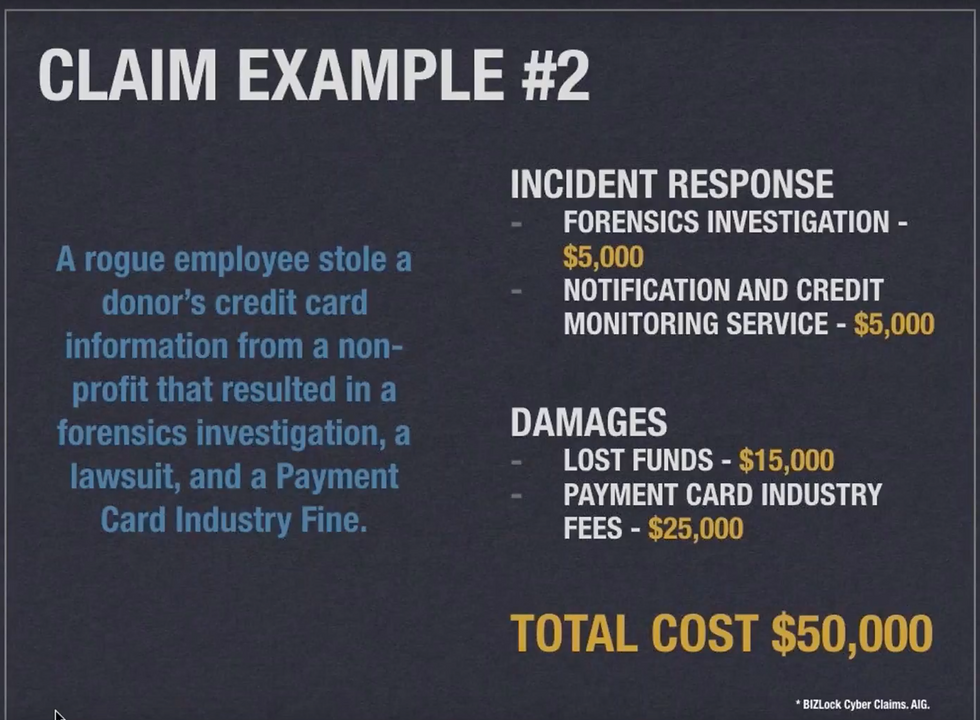
Disgruntled employees
“Don’t I already have cybersecurity coverage?”
Probably not – traditional commercial general liability and property insurance policies typically exclude cyber risks from their terms, leading to the emergence of cybersecurity insurance as a “stand-alone” line of coverage. That coverage provides protection against a wide range of cyber incident losses that businesses may suffer directly or cause to others, including costs arising from data destruction and/or theft, extortion demands, hacking, denial of service attacks, crisis management activity related to data breaches, and legal claims for defamation, fraud, and privacy violations.
“I do have Cybersecurity Coverage. Do I have the right coverage?”
When designing your policy, you and your insurance agent should have assessed what your actual risk might be, and should have considered the following:
Expenses you’ll incur if you’re breached such as the cost of notifying the individuals affected, and PCI (Payment Card Industry) fines, and costs for data recovery. These can be very expensive.
Damages you’ll incur from stolen identities, lost information, and the loss of trade secrets.
Here are some examples of what could occur:
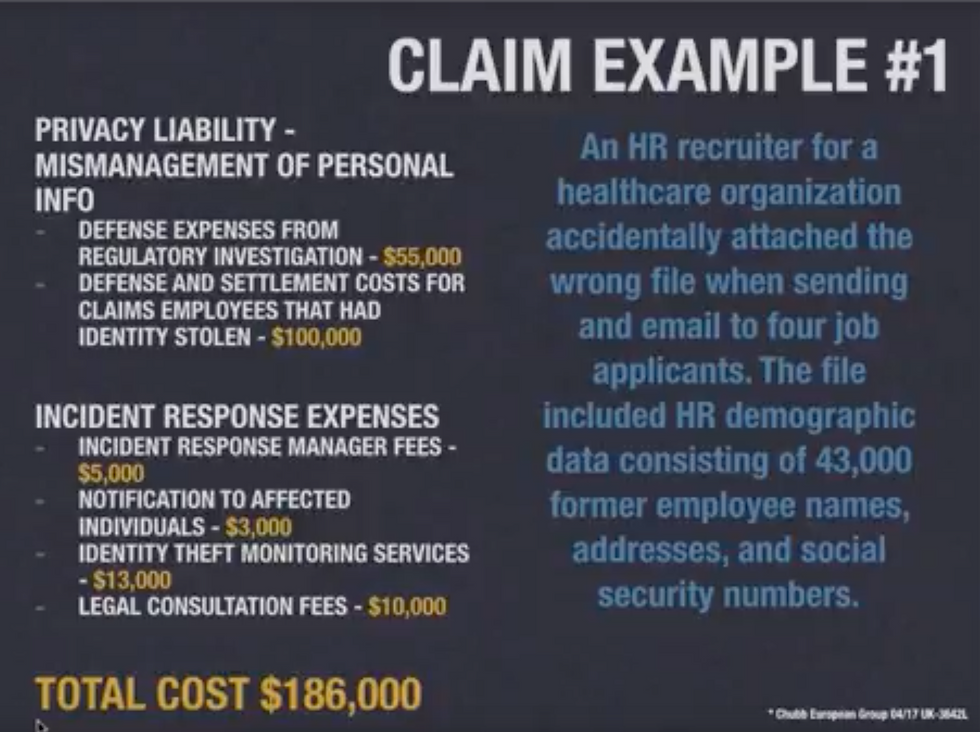
On average, each piece of stolen data costs businesses $250.
If you have 4,000 customers, this equates to $1 Million that you’ll have to spend! Not to mention the damage to your reputation it will cause with lost customers and losing the ability to gain new ones.
What you must include in your Cybersecurity Policy:
1. Third-Party Coverages
Third-Party Coverages pay others for damages and expenses when you (the policyholder) are liable. It pays out to another person due to your failure to secure their data. It should include:
Content Liability: If your business has any kind of online presence, it’s important to obtain a Cybersecurity Policy that includes Content Liability. It provides coverage against defamation and invasion of privacy on web pages like Facebook, LinkedIn and for company blogs, or from copyright infringements from your company website.
Privacy Liability: This would cover your business’s liability for a data breach where your customers’ personal information was exposed or stolen by a hacker via access to your electronic network. It covers the expenses you could incur such as those from defending claims by state regulators, any fines or penalties, notification expenses, credit-monitoring costs, and any losses resulting from identity theft.
Security Breach Liability: This helps to cover expenses incurred by a data security breach for things like legal fees, public relations, identity protection solutions, liability and more depending on the insurance coverage you need.
2. First-Party Coverage
This will pay you for damages incurred such as:
Security breach expenses – the costly expenses to notify people.
Loss of business income – if you have to shut down your business for a few days, weeks or months, and to cover things like to your rent, utility bills, etc.
Extortion threats and ransom payments – if you have to pay money for your data to be released when a hacker steals it.Public relations expenses – PR costs for damage control to your reputation.Replace and restore lost data – any costs you incur for this.
Fraudulent impersonation – This could happen if one of your employees willingly or mistakenly sends your money to someone impersonating a vendor or someone you regularly send money to. Many cybersecurity policies don’t cover this unless it includes specific endorsements and coverages.
3. The Correct Limits
For example, if you have 4,000 clients and their data is stolen at $250 per client, your coverage should be no less than $1 million.

Know your risks and adequately protect against them.
Sit down with your team and your insurance broker and make a list of anything your business could be exposed to. Think about how you do business every day, how you interact with the Internet, how your business interacts with computers, and consider your risk points. List anything that would devastate your business if you lost it. Make sure your policy covers all these things and protects you.
Your IT Managed Service Provider should be protecting your data on the front end, but you always want to have insurance coverage on the back end if a breach occurs.

Your IT Managed Services Provider should provide all these technology solutions for you. However, the human error component can’t be covered with technical solutions. So, it’s important to have your MSP conduct Cybersecurity Awareness Training for your staff to teach them how to recognize hacking attempts and what to do if one comes their way.


